Medusa ransomware has become one of the most menacing cyber threats globally, targeting organizations and businesses with relentless precision. This sophisticated malware encrypts critical data and demands exorbitant ransoms for its release. Understanding the nature of Medusa ransomware and the role of CISA (Cybersecurity and Infrastructure Security Agency) in combating such threats is essential for safeguarding your digital assets.
As cyberattacks grow increasingly sophisticated, it is crucial for individuals and organizations to stay informed about emerging threats like Medusa ransomware. In this article, we will explore the origins, mechanisms, and prevention strategies related to Medusa ransomware, with a focus on the guidance provided by CISA. By understanding the full scope of the threat, you can take proactive measures to protect your systems.
By the conclusion of this article, you will possess a comprehensive understanding of how Medusa ransomware operates, the risks it poses, and the steps you can take to secure your systems. Let’s delve into this critical issue together.
Read also:Exploring The Unique Traits Of April 21 Zodiac A Comprehensive Guide
Table of Contents
- Understanding Medusa Ransomware
- CISA's Role in Fighting Ransomware
- The Origins of Medusa Ransomware
- The Mechanics of Medusa Ransomware
- The Impact on Businesses and Individuals
- Strategies for Prevention
- Detection and Response Techniques
- Options for Data Recovery
- Legal Considerations of Ransomware Attacks
- Emerging Trends in Cybersecurity
- Conclusion
Understanding Medusa Ransomware
Exploring the Threat Landscape
Medusa ransomware exemplifies the alarming trend of cybercrime where malicious actors deploy advanced encryption techniques to hold valuable data hostage. Unlike traditional malware, ransomware specifically targets sensitive information, making it an attractive and lucrative endeavor for cybercriminals.
The emergence of Medusa ransomware aligns with the rise of sophisticated attack vectors. Cybercriminals now employ tactics such as phishing emails, exploit kits, and unpatched vulnerabilities to infiltrate systems. Consequently, organizations must prioritize robust cybersecurity measures to counteract these threats effectively.
Medusa ransomware is particularly challenging due to its adaptability and ability to evade detection. Its developers continuously refine the malware to bypass traditional security protocols, posing a persistent challenge for IT professionals worldwide.
CISA's Role in Fighting Ransomware
Guidance and Resources from CISA
The Cybersecurity and Infrastructure Security Agency (CISA) plays a pivotal role in addressing the ransomware epidemic. CISA provides actionable guidance, resources, and tools to help organizations mitigate the risks associated with Medusa ransomware and other forms of cyberattacks.
Key initiatives by CISA include:
- Issuing alerts and advisories to warn about emerging threats.
- Offering best practices for securing networks and endpoints.
- Collaborating with international partners to enhance global cybersecurity efforts.
CISA's commitment to fostering a resilient digital ecosystem underscores the importance of staying informed and proactive in the face of evolving cyber threats. Organizations can leverage CISA's resources to strengthen their defenses and reduce their vulnerability to ransomware attacks.
Read also:Experience The Magic Capturing The Perfect Ballpark Moments
The Origins of Medusa Ransomware
Tracing the Evolution of Medusa
Medusa ransomware first emerged in 2020, quickly gaining notoriety for its advanced encryption algorithms and stealthy deployment methods. Its creators are believed to be part of a well-organized cybercriminal syndicate with ties to Eastern Europe, making it a globally recognized threat.
One of the standout features of Medusa ransomware is its use of polymorphic code, enabling it to alter its signature and evade detection by antivirus software. This adaptability has positioned Medusa as a formidable adversary for cybersecurity professionals worldwide.
Understanding the origins of Medusa ransomware is critical for developing effective countermeasures. By analyzing its evolution, experts can identify patterns and anticipate future developments in the ransomware landscape, ultimately improving cybersecurity strategies.
The Mechanics of Medusa Ransomware
Inside the Attack Process
Medusa ransomware operates through a multi-stage attack process that begins with gaining initial access to a target system. Common entry points include phishing emails, malicious attachments, and unpatched vulnerabilities, making user awareness and system updates crucial for prevention.
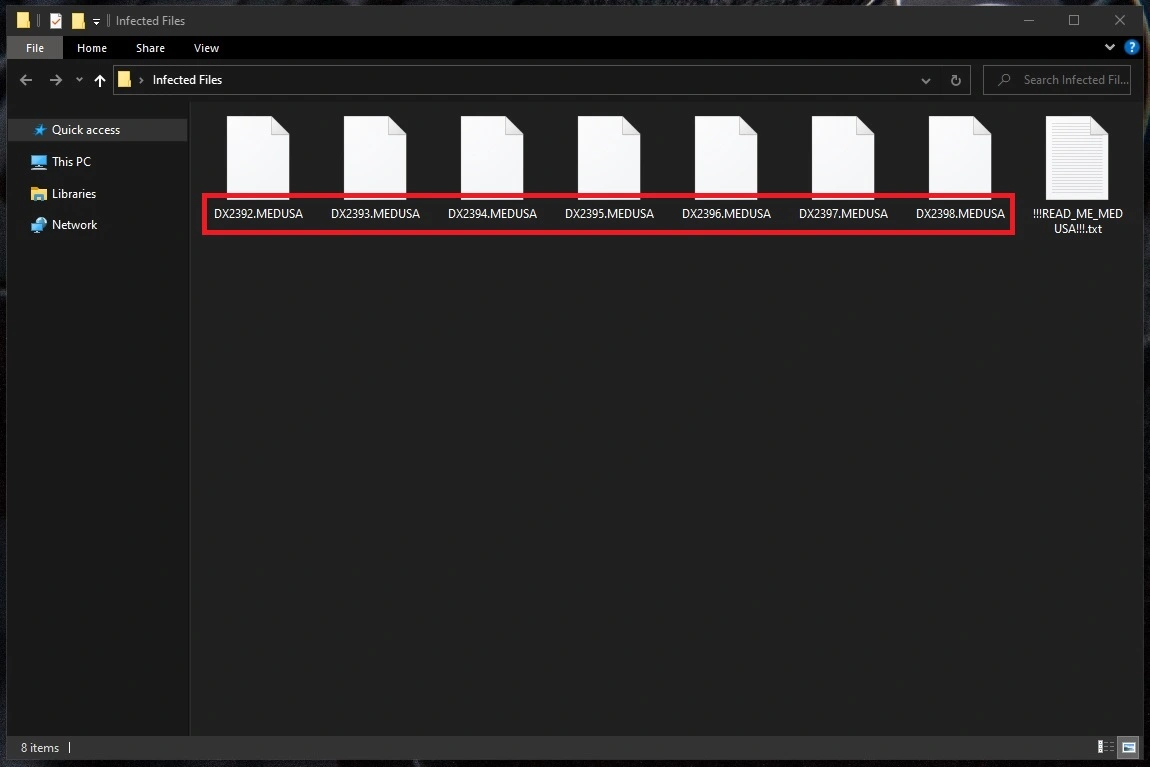
Once inside, the malware conducts reconnaissance to identify valuable data and map the network structure. It then deploys its encryption payload, locking files and demanding a ransom in exchange for the decryption key. This process is swift and can cause significant damage in a short period.
Key characteristics of Medusa ransomware include:
- Use of robust encryption algorithms such as AES-256.
- Ability to spread laterally across networks, amplifying its impact.
- Integration with command-and-control servers for remote management, ensuring continuous control over infected systems.
By understanding the mechanics of Medusa ransomware, organizations can implement targeted defenses to disrupt the attack lifecycle and minimize the risk of infection.
The Impact on Businesses and Individuals
Evaluating the Consequences
The consequences of Medusa ransomware extend far beyond financial losses. Businesses face reputational damage, operational disruptions, and potential regulatory penalties. Individuals may experience the loss of personal data, leading to identity theft and other long-term repercussions.
According to a report by Cybersecurity Ventures, ransomware attacks are projected to cost businesses over $20 billion globally by 2021. This staggering figure underscores the urgency of addressing the Medusa ransomware threat and implementing comprehensive cybersecurity measures.
Moreover, the psychological toll on victims cannot be overlooked. The stress and anxiety caused by a ransomware attack can have lasting effects on both individuals and organizations, underscoring the need for robust prevention and response strategies.
Strategies for Prevention
Building a Strong Defense
Preventing Medusa ransomware requires a multi-layered approach that combines technical controls, user education, and organizational policies. Below are some effective prevention strategies:
- Regularly update software and apply security patches to address known vulnerabilities.
- Implement robust access controls and network segmentation to limit the spread of malware.
- Conduct employee training on recognizing phishing attempts and other common attack vectors.
- Enable endpoint protection solutions with advanced behavioral analysis capabilities to detect and respond to threats in real-time.
Organizations should also establish a comprehensive incident response plan to ensure swift action in the event of a breach. This proactive approach can significantly reduce the impact of a Medusa ransomware attack and enhance overall cybersecurity posture.
Detection and Response Techniques
Identifying and Neutralizing Threats
Early detection is critical in mitigating the effects of Medusa ransomware. Advanced threat detection tools, such as intrusion detection systems (IDS) and security information and event management (SIEM) platforms, can help identify suspicious activity on the network and alert security teams promptly.
Response techniques include isolating infected systems to prevent further spread, containing the malware's lateral movement, and eradicating the threat from the environment. Incident response teams should collaborate closely with cybersecurity experts to ensure a coordinated and effective response, minimizing downtime and data loss.
Regularly testing detection and response capabilities through tabletop exercises and simulations can enhance an organization's readiness to handle Medusa ransomware attacks and improve overall cybersecurity resilience.
Options for Data Recovery
Restoring Access to Encrypted Data
In the event of a successful Medusa ransomware attack, organizations have several options for recovering their data. The most reliable method is restoring from secure and regularly updated backups, ensuring minimal disruption to operations.
Alternatively, decryption tools may be available for older variants of Medusa ransomware. However, relying on these tools can be risky, as newer versions often incorporate countermeasures to prevent decryption, rendering them ineffective.
It is strongly advised against paying the ransom, as it encourages further criminal activity and does not guarantee the return of data. Instead, organizations should focus on strengthening their defenses and improving their recovery processes to mitigate future risks.
Legal Considerations of Ransomware Attacks
Navigating the Legal Landscape
Ransomware attacks raise significant legal and ethical concerns. Organizations that fall victim to Medusa ransomware may face regulatory scrutiny, particularly if sensitive customer data is compromised, leading to potential fines and legal action.
Key legal considerations include compliance with data protection laws such as GDPR and HIPAA, as well as reporting obligations under applicable regulations. Organizations must also assess their insurance coverage to determine if cyber incidents are covered, ensuring financial protection in the event of a breach.
Working with legal experts and cybersecurity professionals can help organizations navigate the complex legal landscape surrounding ransomware attacks. This collaboration ensures a comprehensive and compliant response to the threat, protecting both the organization and its stakeholders.
Emerging Trends in Cybersecurity
Anticipating the Next Wave of Threats
The cybersecurity landscape is constantly evolving, with new threats emerging alongside advancements in technology. As artificial intelligence and machine learning become more prevalent, cybercriminals are likely to leverage these tools to enhance their attack capabilities, making future threats even more sophisticated.
To stay ahead of Medusa ransomware and other emerging threats, organizations must adopt a proactive and adaptive approach to cybersecurity. This includes investing in cutting-edge technologies, fostering a culture of security awareness, and participating in information-sharing initiatives to stay informed about the latest threats.
By anticipating future trends and preparing for the worst-case scenarios, organizations can build resilience against the ever-evolving ransomware threat landscape, ensuring the safety and integrity of their digital assets.
Conclusion
In conclusion, Medusa ransomware represents a significant challenge for businesses and individuals worldwide. Understanding its origins, mechanisms, and impact is essential for developing effective prevention and response strategies. The guidance provided by CISA plays a vital role in addressing this threat and promoting a safer digital environment.
We encourage readers to take action by implementing the prevention strategies outlined in this article and staying informed about the latest developments in cybersecurity. Share this article with your colleagues and explore other resources to enhance your knowledge and preparedness. Together, we can combat the Medusa ransomware threat and protect our digital assets for the future.